This post addresses another important aspect of cloud security – the network, both within the Cloud Service Provider and the user organisation’s connection to the Cloud Service Provider. As network security is specific to each cloud service provider, this document concentrates on Amazon Web Services (AWS) and provides an overview of some of the key security services and resources it provides to cloud architects.
Network and Security in Amazon Web Services (AWS)
The network infrastructure in AWS contains the following components:
- Virtual Private Cloud (VPC) – A logical isolated section of the AWS cloud for a specific customer to launch resources.
- Subnet – A segment of a VPC’s IP address range where you can place groups of isolated resources.
- Network Access Control List (ACL) – A layer of security for a customer VPC that acts as a firewall for controlling traffic in and out of one or more subnets.
- Security Group – A virtual firewall for an instance to control inbound and outbound traffic.
- Internet Gateway – A VPC component that allows communication between instances inside a VPC and the internet.
- NAT Gateway – A component that allows instances in a private subnet to connect to the internet without allowing connections to be initiated from the internet.
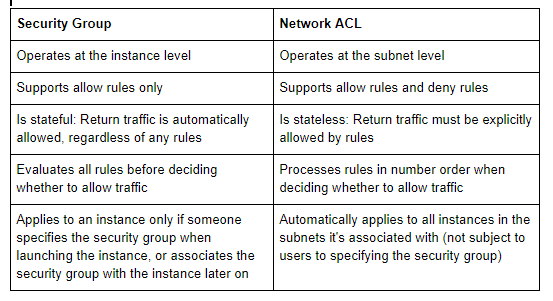
Comparison of Security Groups and Network ACLs
AWS provides firewalling capability for inbound and outbound traffic using Security Groups and Network ACLs.
References:
Instructions for creating a new Network Access Control List:
https://docs.aws.amazon.com/vpc/latest/userguide/vpc-network-acls.html#nacl-tasks
Best practices for Network ACL:
https://docs.aws.amazon.com/vpc/latest/userguide/vpc-recommended-nacl-rules.html
Instructions for creating a new Security Group:
https://docs.aws.amazon.com/vpc/latest/userguide/VPC_SecurityGroups.html#WorkingWithSecurityGroups
Best practices for Security Groups:
Instructions for creating a new Internet Gateway:
https://docs.aws.amazon.com/vpc/latest/userguide/VPC_Internet_Gateway.html#working-with-igw
Instructions for creating a NAT gateway:
https://docs.aws.amazon.com/vpc/latest/userguide/vpc-nat-gateway.html#nat-gateway-working-with
AWS Security Best Practices:
https://d1.awsstatic.com/whitepapers/compliance/AWS_CIS_Foundations_Benchmark.pdf
About the author
Eyal Estrin, cloud architect.
cloud architect.

